

Advanced DLL injection tool with 6 injection methods.
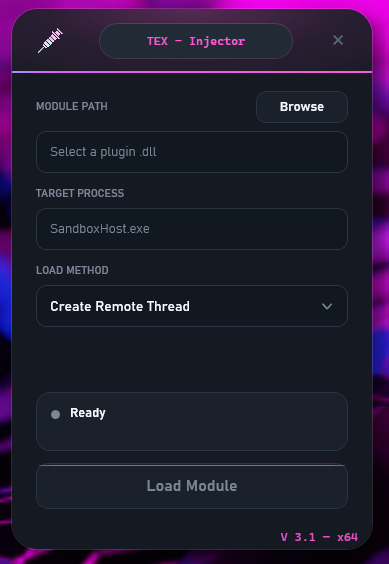
TEX - Injector is a lightweight tool for injecting DLLs into processes you own - for testing, debugging, and development.
What's new in V3: All injection logic now runs in-process - no more separate Host.exe. This means a single ~150 MB standalone EXE with everything included.
Supports x64 and x86 (WoW64) targets. Choose from 6 different load methods depending on your needs.
Always abide by legal guidelines and use only on processes you own.
Kussi Schatzi A💜
Classic approach via CreateRemoteThread + LoadLibraryW.
Lower-level kernel thread creation via ntdll. Bypasses some user-mode hooks.
Queues an APC to all target threads. Execution happens when the thread enters alertable state.
Loads a DLL entirely from memory - no disk writes in the target process.
Calls NtCreateThreadEx via raw syscall (bypasses ntdll completely).
Suspends a target thread, redirects execution to load the DLL, then restores context.
GUI Mode (Portable):
tex-injector-x64.exe or tex-injector-x86.exe.notepad.exe), select an injection method, and click Inject.Launcher Mode (TEX-Injector.exe):
TEX-Injector.exe next to the x64/ and x86/ folders.TEX-Injector.exe - it detects your OS architecture and launches the matching portable build.Injection Method IDs (for developers):
0 = CreateRemoteThread
1 = NtCreateThreadEx
2 = QueueUserAPC
3 = ReflectiveDLL
4 = DirectSyscall
5 = ThreadHijack
TexLoader.Host.exe.AllocConsole for injection verificationTexLoader.Host.exe process architecture